Network Record Check – 5545686316, Secretangelholli, 662903727, Vtlpyfybz, 3792795496
Network record traces reveal a chain of identifiers and aliases that map to potential user activity. The numbers—5545686316, 662903727, 3792795496—and the aliases Secretangelholli and Vtlpyfybz form a mosaic of digital footprints. Investigators note patterns, gaps, and timestamps that suggest routine behavior or irregular bursts. The data raises questions about collection, consent, and retention. The findings point to governance challenges and evolving privacy norms, leaving a concrete path forward unclear and accountability unsettled.
What Network Record Check Reveals About Traces
Network record checks illuminate the digital breadcrumbs left by a subject, tracing patterns that endure beyond surface activity. Investigators map sequences of connections, timestamps, and locations, revealing consistent habits and anomalous bursts.
The data expose privacy implications and outline data retention timelines, clarifying how long information persists. Such traces, though fragmentary, enable informed judgments about behavior, risk, and potential privacy trade-offs.
Decoding Identifiers: 5545686316, 662903727, 3792795496 and Aliases
Decoded identifiers function as the numeric fingerprints of digital activity, each sequence—5545686316, 662903727, 3792795496—carrying a distinct footprint across networks and logs. Investigative persistence reveals how decoding identifiers exposes pathways to aliases decoding; semantics shift as aliases map to origins. Privacy implications surface through persistent data traces, prompting scrutiny of freedom-minded users seeking control over identity and traceability.
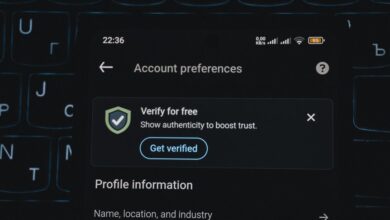
How Records Are Collected and What They Mean for Privacy
How records are collected and what they mean for privacy is best understood by tracing the data lifecycle from capture to retention. Investigators examine data sources, consent scope, and automated collection practices, revealing privacy implications. Emphasis rests on data minimization, robust security considerations, and clear accountability implications, ensuring transparency while highlighting potential risks, controls, and responsibilities within evolving regulatory landscapes.
From Footprints to Findings: Interpreting Behavior, Security, and Accountability
From the preceding discussion of how records are collected and what they mean for privacy, the focus shifts to how those traces become actionable insights. Analysts map footprints to patterns, distinguishing suspicious from normal behavior, while maintaining accountability. Sensitive data and user privacy hang beside legal implications, data retention, and governance, guiding enforceable decisions without erasing individual autonomy.
Frequently Asked Questions
How Reliable Are Network Record Checks Across Platforms?
Network record checks show limited reliability due to variability across systems, with noticeable reliability variance and platform interoperability gaps; they occasionally converge on accurate results, yet inconsistencies persist, demanding persistent verification and investigative rigor for freedom-seeking audiences.
Do IDS Imply Real-World Identity Beyond the Study?
Investigation reveals IDs do not reliably prove real-world identities beyond the study. Coincidence underscores blurred boundaries; user privacy implications loom as platform cross compatibility expands, yet safeguards vary. Detachment persists, guiding readers toward cautious, freedom-oriented scrutiny.
Can Data Be Updated After Initial Collection?
Data updates can occur after initial collection, yet collection integrity demands rigorous provenance, versioning, and audit trails; investigators persistently track changes, ensuring transparency, reproducibility, and freedom to verify evolving datasets without compromising ethical boundaries.
What Safeguards Protect User Anonymity in Results?
Anonymity safeguards include robust privacy controls and verifiable data provenance, ensuring results conceal identifying details while preserving source integrity; investigators note layered anonymization, access logs, and audit trails, maintaining accountability for disclosures and user-directed privacy preferences throughout analyses.
Are There Legal Limits to Sharing Network Traces Publicly?
A single question lingers: yes, there are legal limits to publicly sharing network traces. The inquiry examines privacy implications and data ownership, balancing transparency with protection; investigators insist on cautious disclosure, identifying censored details and safeguarding individual privacy.
Conclusion
The investigation closes with a meticulous stitching of digital footprints into a coherent trace. Each identifier and alias functions as a breadcrumb, revealing patterns without overstepping privacy boundaries. The method remains disciplined, balancing data utility with consent and retention limits. While the traces point to plausible origins and behaviors, they also illuminate gaps where verification is needed. In sum, the mosaic speaks of accountability and governance—a lantern in a complex network, guiding lawful, cautious decision-making. A careful scribe, watching.