Data Node Start 513-813-7884 Exploring Accurate Phone Discovery
Data Node Start 513-813-7884 explores accurate phone discovery by outlining the identification, cataloging, and reachability of devices within governed privacy boundaries. The discussion weighs verification methods, including pattern matching and cross-source reconciliation, against speed and resource constraints. It emphasizes provenance, consent, and accountability to support reproducible results. The implications span privacy safeguards and compliant outreach, yet practical gaps remain that invite careful consideration of implementation challenges and governance.
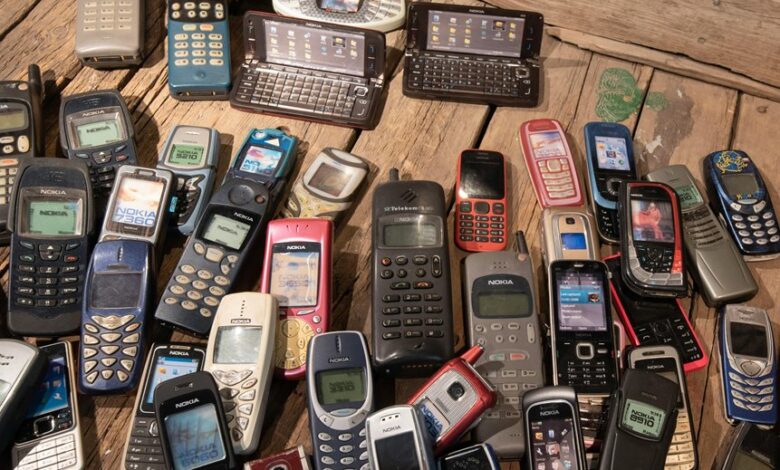
What Is Accurate Phone Discovery and Why It Matters
Accurate phone discovery refers to the process of reliably identifying and cataloging phones connected to a network or system, including their model, status, and reachability.
This framework supports governance by enabling consistent inventory and risk assessment, guiding resource allocation.
Accuracy assessment and Verification methods shape confidence levels, reducing ambiguities, supporting compliance, and informing design choices while preserving operator autonomy and system resilience.
How Phone Data Is Verified: Techniques and Trade-offs
Verification of phone data combines multiple techniques to confirm identity, status, and reachability while balancing speed, accuracy, and resource use. The section outlines data verification methods such as pattern matching, cross-source reconciliation, and validation checks, while noting trade-offs like latency and coverage. It emphasizes ethical sourcing and transparent provenance as core constraints guiding reliable, freedom-conscious data practices.
Building a Trustworthy Discovery Pipeline: Practices and Ethics
Developing a trustworthy discovery pipeline requires a disciplined integration of validation, provenance, and ethics to ensure reliable outcomes. The approach emphasizes rigorous data lineage, transparent governance, and reproducible results. Privacy by design guides architecture, minimizing exposure and risk. Consent frameworks codify user autonomy, aligning collection, storage, and usage with declared preferences and legal standards, while ongoing audits sustain accountability and public trust.
Real-World Use Cases: Outreach, Fraud Prevention, and User Empowerment
Real-World Use Cases illustrate how a robust discovery pipeline translates into tangible outcomes across outreach, fraud prevention, and user empowerment. This analysis evaluates privacy safeguards, consent mechanisms, identity verification, and data minimization as core features. Outcomes include compliant engagement, reduced risk, and empowered participants. Structured processes balance accessibility with protection, enabling responsible experimentation while preserving individual autonomy and freedom.
Conclusion
Conclusion:
The investigation supports the core theory: accurate phone discovery hinges on rigorous verification, transparent provenance, and privacy-conscious governance. A structured pipeline—combining pattern matching, cross-source reconciliation, and validation checks—yields reliable model, status, and reachability data while minimizing exposure. Ethical safeguards, consent, and accountability frameworks enhance trust and reproducibility. Real-world impact materializes as improved outreach, reduced fraud, and empowered users, reinforcing that speed must be balanced with rigorous governance.







