Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
A structured review of account activity for identifiers 8285431493, mez68436136, 9173980781, 7804091305, and IP 111.90.150.204l is proposed. The examination will map usage over time, identify peak access periods, and quantify interaction frequency while preserving privacy and data minimization. Correlations between feature adoption and activity trajectories will be explored, with cross-platform consistency assessed and governance implications highlighted. The goal is to reveal patterns and anomalies in a traceable, auditable manner, inviting closer scrutiny of potential governance gaps and control gaps.
What Account Data Review Reveals About Usage Patterns
Account data reviews illuminate how usage evolves over time, revealing patterns such as peak activity periods, frequency of access, and correlation with feature adoption.
The review delineates account activity trajectories, informs data governance practices, and clarifies user behavior drivers.
It also highlights device equity implications, guiding equitable access considerations while maintaining objective, meticulous assessment of behavioral trends and lifecycle transitions.
Detecting Security Posture and Anomalies Across Platforms
Detecting security posture and anomalies across platforms requires a structured, data-driven approach that contrasts platform-specific telemetry with unified security baselines. The analysis traces deviations in configuration, access patterns, and event timelines, enabling comparative risk scoring.
Cross-platform anomaly detection emphasizes consistency, governance, and traceability, ensuring transparent visibility into gaps and resilience, while preserving freedom to adapt controls to evolving threat landscapes.
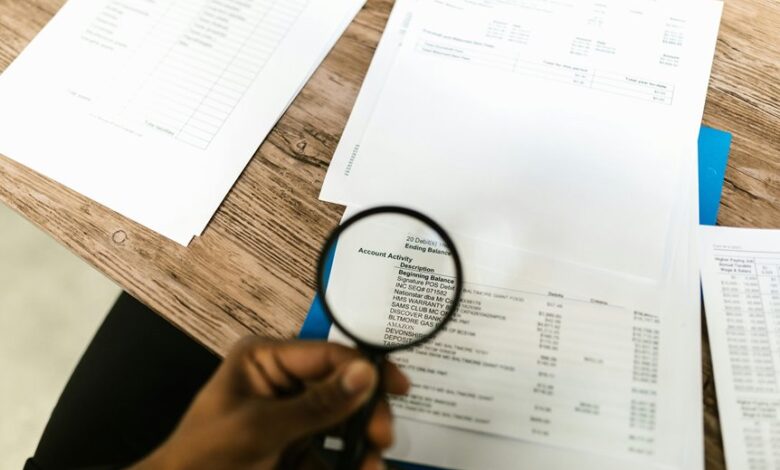
Practical Steps for Auditing Activity by Identifier and IP
Auditing activity by identifier and IP requires a disciplined, methodical workflow that links user or service identifiers to network endpoints and access events. The process emphasizes traceability, standardized logging, and cross-system correlation to reveal patterns in data governance and user behavior. Analysts isolate anomalies, document findings, and maintain defensible records while preserving privacy and operational efficiency for informed decision-making.
Tightening Controls Without Slowing Users Down
Tightening controls without slowing users down requires balancing security with user experience, leveraging targeted, data-driven policies that preserve workflow efficiency while reducing risk.
The analysis emphasizes data minimization and streamlined user verification, applying precise, minimally invasive checks.
Frequently Asked Questions
How Is Data Anonymized in the Review?
Data anonymization occurs by removing identifiers and aggregating fields to preserve audit scope; sensitive details are replaced with pseudonyms, while relevant metrics remain analyzable. The approach is iterative, ensuring compliance, transparency, and findings remain within audit scope.
Are External Apps Included in the Audit Scope?
External apps are included in the audit scope, subject to defined criteria and risk-based prioritization; satire opens with a wary wink toward compliance, followed by a precise, analytical assessment of coverage, exclusions, and governance implications for freedom-minded stakeholders.
How Often Are Reviews Automatically Triggered?
Review cadence is system-driven and occurs automatically at defined intervals, with exceptions requiring manual initiation; data stewardship governs scope, while audits emphasize consistency, traceability, and objective verification, supporting a framework that balances autonomy and accountability for stakeholders.
What Are Acceptable Risk Mitigation Trade-Offs?
Acceptable risk trade-offs depend on context; prudent balancing favors data anonymization, minimizing exposure while preserving utility. The approach weighs potential harms against operational needs, documenting assumptions, and ensuring ongoing review, transparency, and defensible justification for risk tolerance levels.
Can Users Request Data Export or Deletion?
Why not clarify: can users request data export or deletion? Yes, individuals may initiate data export and deletion requests, though procedures, verification steps, and retention policies determine scope, timing, and compliance, reflecting a careful, transparent, freedom-respecting approach.
Conclusion
The review frames usage as a delicate weather map, tracing each identifier’s currents across time and platforms with disciplined precision. A pattern emerges: peaks align with feature adoption cycles, while cross-system correlations illuminate governance threads and potential risk pockets. Anomalies glow as warning flares, warranting deeper inquiry without compromising privacy. The analysis balances data minimization with traceable logging, offering a lucid, objective trajectory for tightening controls while preserving user experience.