System Entry Analysis – νεςσμονευ, Rodotrollrdertozax, 6983286597, Why Is shuguntholl2006 About, steelthwing9697

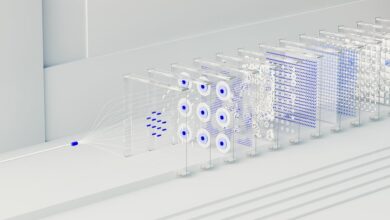
System Entry Analysis integrates governance, provenance, and access considerations to trace inputs, transformations, and outputs across systems. It anchors accountability to unique identifiers, alias governance, and security labeling to prevent misalignment. By examining design choices and interoperability, the approach assesses real-world implications, coherence across platforms, and the risks of fragmentation. The framework invites closer scrutiny of how labels, identifiers, and validation cycles shape outcomes, leaving a clear path for further inquiry into its practical viability.
What System Entry Analysis Really Is and Why It Matters
System Entry Analysis is a framework for examining how data and metadata enter a system, are transformed, stored, and retrieved, along with the governance that guides those processes. It structures evaluation of inputs, transformations, and outputs, emphasizing clarity, traceability, and accountability. The approach enables a two word discussion idea, unrelated topic, guiding stakeholders toward disciplined inquiry, policy alignment, and auditable, freedom-supporting decision making.
Mapping the Identity Mosaic: Decoding Unique Identifiers and Names
To build upon the prior discussion of System Entry Analysis, this section dissects how unique identifiers and names function as the backbone of data provenance.
The analysis identifies systematic patterns in label provenance, highlighting how identifiers mismatch can undermine traceability.
It evaluates alias governance structures, and conducts a focused risk assessment to illuminate governance gaps and accountability.
Access, Security, and Design: How Labels Shape Real-World Implications
Access controls and design decisions directly influence how labels function in practice, shaping both security posture and user interaction.
The analysis examines how identity labeling and security labeling encode permissions, enforce boundaries, and steer workflow choices.
Designers balance flexibility with risk, ensuring legibility, audibility, and reversibility.
Real-world implications emerge in accountability, interoperability, and usable segregation across systems, roles, and environments.
Patterns, Pitfalls, and Practices: Building a Coherent Framework From Fragments
The fragmentation of labeling and control mechanisms across disparate systems poses a challenge for coherence. Patterns emerge from modular fragments, revealing recurring structures and assumptions. Pitfalls include overgeneralization, fragmented governance, and misaligned incentives. Practices focus on mapping dependencies, formalizing interfaces, and iterative validation. A coherent framework requires disciplined integration, transparent criteria, and governance that aligns fragments toward shared objectives and meaningful interoperability.
Frequently Asked Questions
How Does System Entry Analysis Affect Everyday Privacy Differently From Policy?
System entry analysis shapes everyday privacy by revealing operational practices beyond formal policy, highlighting privacy gaps and reinforcing data governance. It differentiates practical protections from statutory rules, guiding individual autonomy while balancing transparency and collective accountability.
Can Identifiers Exist Without Corresponding User Names or Roles?
Yes, identifiers can exist without user names or roles, functioning as abstract references. However, identities without context risk ambiguity; labels without accompanying metadata hinder interpretation, while enabling privacy-preserving analysis and freedom-oriented, granular data governance.
What Are Hidden Costs of Implementing Strict Labeling Systems?
A striking 42% of projects overrun budgets due to labeling systems. Hidden costs include workflow disruption, maintenance, compliance overhead, and training time, which collectively erode efficiency and freedom as processes become constrained and monitoring intensifies.
Do Cultural Biases Affect Interpretation of Identity Fragments?
Cultural perception influences interpretation of identity fragments, shaping bias interpretation through historic frameworks and social norms. The assessment reveals systematic variance, suggesting that context, provenance, and communicative aims modulate meaning, while emphasizing analytic rigor and freedom-respecting objectivity.
How Resilient Are Analyses to Synthetic or Forged Data Inputs?
Analytically, resilience is contingent on methods demonstrating robustness to synthetic or forged data. The truth-seeking process hinges on resilience testing and data provenance, enabling structured evaluation and disciplined adaptation while preserving audience autonomy and interpretive freedom.
Conclusion
In sum, the analysis reveals a fragile lattice where identifiers, labels, and access rules must harmonize to prevent misalignment. Each fragment—inputs, transformations, outputs—carries latent risks that only disciplined governance can uncover. Yet the coherence demanded by interoperability remains elusive, pending ongoing validation. As designs evolve, the suspense centers on whether systems will sustain accountability, reveal provenance transparently, and resist fragmentation before the incentives diverge beyond repair. The next validation will decide the fate of coherence.