Neural Flow 2015475477 Cyber Node
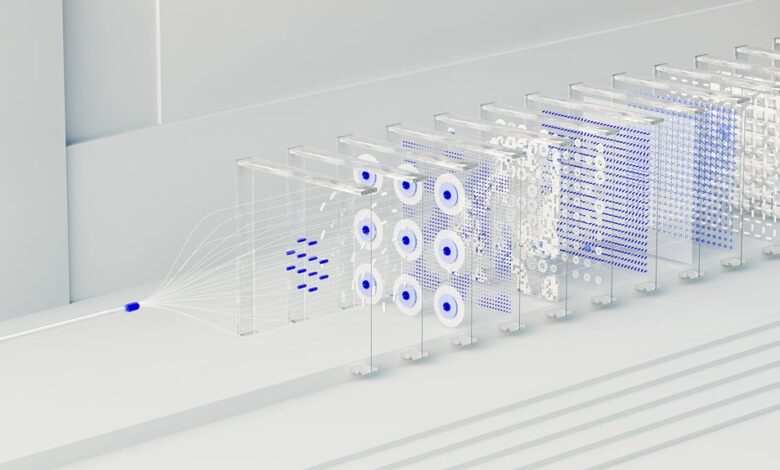
Neural Flow 2015475477 Cyber Node represents an integrated framework for distributed cyber-physical systems. It analyzes real-time traffic as a continuous stream, updating models to reveal efficient decision paths and autonomous network operations. The design emphasizes adaptive defenses and automated responses while preserving operator freedom and system integrity. Performance is monitored with actionable metrics to support reproducible refinement. The approach invites scrutiny of governance, interoperability, and deployment trade-offs, inviting further examination of its practical implications.
What Is Neural Flow 2015475477 Cyber Node and Why It Matters
Neural Flow 2015475477 Cyber Node represents an integrated computational framework designed to manage and optimize data processing across distributed cyber-physical systems. It enables modular coordination, fault resilience, and scalable resource allocation.
The construct emphasizes transparent governance, interoperability, and proactive data routing. In essence, neural flow and cyber node illuminate efficient decision pathways, empowering autonomous networks while preserving operator freedom and system integrity.
How the Cyber Node Learns From Network Traffic in Real Time
One approach is to treat network traffic as a continuous stream of signals that the Cyber Node analyzes to update its internal models in real time. The neural flow enables real time learning by mapping patterns and anomalies to adaptive representations.
Through continuous observation of network traffic, the system refines predictions, compliance checks, and resilience strategies, maintaining autonomous, proactive defense. cyber node.
Implementing Adaptive Defenses: From Threat Detection to Automated Response
Building on the real-time learning of traffic patterns, the focus shifts to turning detections into rapid, automated actions. The discussion analyzes adaptive defenses that translate threat signals into immediate mitigations, reducing latency and human dependency. It emphasizes automated response, vigilant monitoring, and controlled autonomy within network threat scenarios, guided by real time learning to sustain resilient, freedom-forward cyber operations.
Evaluating Performance: Metrics, Pitfalls, and Deployment Best Practices
Evaluating performance in neural flow systems requires a precise framework of metrics, an awareness of common pitfalls, and clear deployment guidelines to ensure reliable operation.
The analysis emphasizes performance metrics as actionable signals, real time learning adaptability, and robust adaptive defenses.
It highlights deployment best practices that minimize drift, ensure reproducibility, and sustain transparency while allowing freedom to iterate and refine system behavior.
Conclusion
In the end, Neural Flow 2015475477 Cyber Node stands poised at a delicate hinge between insight and consequence. Its real-time learning uncovers covert patterns, while adaptive defenses tighten the weave of protection. Yet each autonomous decision echoes through the network’s fabric, inviting scrutiny and anticipation. As metrics sharpen, operators await the next subtle shift—one misreadable cue could redefine risk and resilience. The system remains vigilant, awaiting the moment when proactive governance yields undeniable clarity.