Call Log Verification – Cyberpúerta, Drrodrigoharo, vittenthill49, heimvinec6025, elldlayen854
Call log verification across Cyberpúerta, Drrodrigoharo, Vittenthill49, Heimvinec6025, and Elldlayen854 requires a disciplined approach to provenance, timestamps, durations, participants, and outcomes. The process blends automated checks with auditable lineage and cryptographic seals to deter tampering. It emphasizes data minimization, risk-based validation, and regulatory alignment. The result is a reproducible, verifiable trail whose strengths and limits become clearer as procedures mature, inviting scrutiny on how control points are documented and reconciled.
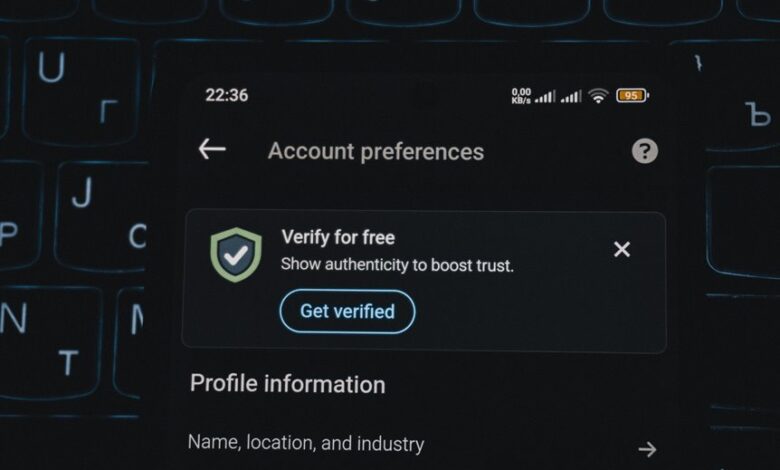
What Is Call Log Verification and Why It Matters
Call log verification is the process of confirming that recorded call data—such as timestamps, durations, participants, and call outcomes—accurately reflects actual events.
This assessment evaluates call log integrity, ensuring traceability verification across records.
It reinforces data provenance by documenting source, changes, and rationale, supporting telecom compliance and auditable workflows while promoting disciplined transparency and freedom through rigorous, objective verification practices.
How to Distinguish Authentic vs. Forged Call Records
Distinguishing authentic from forged call records requires a structured, evidence-based approach that separates legitimate metadata from manipulated entries. The analysis centers on call integrity, data provenance, and tamper detection within verification standards. Researchers compare timestamp consistency, originating numbers, and routing paths, while accounting for dialectical anomalies. Clear criteria enable objective judgments about authenticity, supporting responsible disclosure and freedom through rigorous methodological evaluation.
Practical Methods and Tools for Robust Verification
Practical verification hinges on a structured toolkit that combines data provenance, reproducible procedures, and automated checks. The methodology emphasizes traceable lineage, verifiable timestamps, and tamper-evident records. Analytical controls assess call log integrity and source authentication, deploying cryptographic seals, hash chains, and audit trails. Process-driven verification enables reproducibility, fosters transparency, and supports independent validation within a freedom-respecting analytical framework.
Real-World Scenarios and Best Practices for Trust and Compliance
In real-world operations, trust and compliance hinge on disciplined application of verification practices across diverse scenarios, from regulated financial institutions to public-sector data initiatives.
The approach prioritizes privacy implications, transparent governance, and auditable controls, balancing flexibility with accountability.
Data minimization guides collection and retention, while risk-based verification aligns resources with critical processes, ensuring consistent integrity, traceability, and lawful, auditable outcomes.
Frequently Asked Questions
How Often Should Call Logs Be Audited for Accuracy?
Audits should occur at least quarterly to ensure ongoing accuracy. This call log auditing practice mitigates metadata risk, allowing provenance verification, anomaly detection, and compliance. Systematic review supports transparency while preserving organizational autonomy and data integrity.
What Are Hidden Risks in Metadata Within Call Records?
Hidden risks in metadata within call records include data privacy concerns and metadata leakage, which can reveal call patterns and networks. About 70% of breaches exploit metadata; thus meticulous controls and auditing reduce exposure and preserve user autonomy.
Can Call Log Verification Detect Spoofed Numbers?
Call log spoofing may evade basic checks, but verification can reveal inconsistencies in metadata risks, phone lineage, and timing patterns; systematic cross-checks reduce false positives, though attackers exploit ephemeral identifiers, demanding layered authentication and continuous monitoring for resilience.
Which Regulatory Standards Apply to Call Log Integrity?
Regulatory standards for call log integrity hinge on compliance standards governing traceability and tamper-evidence, such as telecommunication and financial sector rules; audit frequencies ensure ongoing verification, with regulators emphasizing data lineage, access controls, and immutable records.
How to Train Staff to Recognize Unreliable Logs?
Staff training should emphasize anomaly detection, cross-checking entries, and empowered decision-making; log accuracy improves when scenarios are analyzed, standardized templates used, and periodic audits conducted, enabling independent judgment while maintaining compliance and demonstrating rigorous methodical discipline.
Conclusion
Call log verification reveals whether assertions about calls withstand scrutiny under rigorous provenance checks. By tracing sources, timestamps, participants, and outcomes, it tests the theory that tamper-evident, auditable workflows yield trustworthy records. The evidence supports that robust verification reduces risk and enhances compliance, but only when cryptographic seals, transparent amendments, and reproducible lineage are maintained. In sum, the theory holds that methodical verification reveals truth through reproducible, minimal-data verification and disciplined governance.