Technical Entry Check – 18778896510, Pormocarioxa, 18552763505, 8.218.55.158, 7733288433

A technical entry check for identifiers such as 18778896510, 18552763505, 8.218.55.158, 7733288433, and the term Pormocarioxa requires a disciplined assessment of origin, format, and legitimacy. The process emphasizes scope, accountability, and reproducibility, with cross-referencing sources and risk evaluation to flag anomalies early. Structured steps and clear criteria guide the evaluation, while documented findings support incident readiness. The implications for data integrity are significant, and the next assessment steps will reveal critical considerations.
What a Technical Entry Check Entails and Why It Matters
A Technical Entry Check is a structured verification process that assesses the accuracy, completeness, and legitimacy of critical data and identifiers before entry into a system.
The procedure defines scope, roles, and objectives, emphasizing reproducibility and auditability.
It supports risk assessment by identifying anomalies early, facilitating corrective action, and maintaining data integrity.
This disciplined approach enables informed decision-making and resilient information governance.
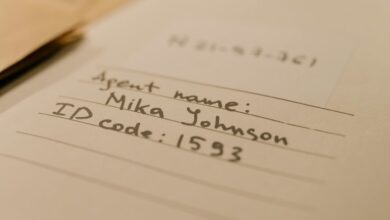
Decoding Identifiers: 18778896510, 18552763505, 8.218.55.158, and 7733288433
Decoding the identifiers 18778896510, 18552763505, 8.218.55.158, and 7733288433 requires a systematic approach to determine their nature, origin, and validity.
The process emphasizes decoding identifiers, validating formats, and cross-referencing sources.
This analysis provides a clear, concise framework for recognition, ensuring secure interpretation without speculative conclusions.
Identifier decoding supports transparent assessment within technical entry checks.
Step-by-Step Framework for Conducting an Efficient Entry Check
How can an efficient entry check be conducted with clarity and rigor? A step-by-step framework organizes actions: define scope, gather data, perform a structured risk assessment, verify sources, and document findings. Each stage supports traceability, minimizes ambiguity, and preserves autonomy. The entry check proceeds methodically, ensuring reproducibility, timely insights, and informed decisions while maintaining emphasis on risk assessment and transparent accountability.
Common Pitfalls and Best Practices in Risk Assessment and Incident Response
Effective risk assessment and incident response require awareness of common pitfalls and the adoption of proven practices. The text identifies misjudging scope, overreliance on automation, and delayed escalation as frequent errors, while emphasizing clear ownership, reproducible data, and regular exercises.
Implementing risk assessment rigor and incident response discipline yields resilience, measurable improvements, and informed decision-making under pressure. Continuous learning sustains operational freedom and security.
Frequently Asked Questions
How to Verify the Source of a Technical Entry Check Request?
Verification involves auditing the request path, corroborating logs, and validating cryptographic signatures; the verification process emphasizes data provenance, ensuring each entry’s origin and integrity before acceptance and downstream processing in a transparent, auditable manner.
What Privacy Safeguards Protect Identifiers Used in Checks?
Privacy safeguards protect identifiers by limiting exposure and encrypting data in transit and at rest. Source verification relies on audit retention and automated checks, while legal implications shape retention periods and access controls, ensuring robust identifiers protection.
Can Checks Be Automated Across Multiple Networks Simultaneously?
Automated cross network verification is feasible, enabling parallel verification across multiple networks. However, operational safeguards, latency considerations, and governance requirements must be addressed to ensure reliability, security, and respect for user autonomy within interconnected infrastructures.
What Are Legal Implications of Recording Entry Check Data?
Recording entry check data implicates privacy laws and consent, with potential compliance and liability exposure; data sovereignty governs storage rights, while incident response protocols shape retention, notification, and audit trails within jurisdictional boundaries.
How Often Should Audit Logs for Checks Be Retained?
Audit retention should align with regulatory demands and internal policy, typically ranging from one to seven years. Check verification logs require periodic review; longer retention supports audits, while shorter periods reduce risk and storage burdens.
Conclusion
In the quiet ledger of risk, the identifiers stand like quiet sentinels at a doorway. Each mark—18778896510, 18552763505, 8.218.55.158, 7733288433, and Pormocarioxa—is a beacon guiding traceability through fog. A disciplined entry check acts as a steel hinge, turning with accountability and reproducibility. Through defined scope and cross-referenced sources, anomalies are spotted early, decisions are grounded, and incidents are contained, leaving a clear, auditable path for future inquiries.