Signal Core Start 512-768-9531 Revealing Verified Contact Research

Signal Core Start 512-768-9531 reveals a methodology that questions how contact identifiers are labeled and interpreted in Signal threads. The approach demands verification through metadata, timing, and reproducible evidence rather than accepting self-proclaimed labels. It probes gaps between trust signals and actual cryptographic attestations, urging transparent criteria and documented rationales. The result is a disciplined, evidence-based stance that invites scrutiny, but leaves open questions about where the next clues will come from and how they will shift conclusions.
What Signal Core Start 512-768-9531 Actually Represents
What does the designation “Signal Core Start 512-768-9531” actually signify? The phrase prompts rigorous inquiry rather than assumption, focusing on subtopic relevance and the precise functions behind a code. It invites scrutiny of how signals are labeled, parsed, and interpreted. Skeptical verification pitfalls reveal gaps between attribution and actuality, urging disciplined evaluation before claimed legitimacy or operational meaning.
How Researchers Verify Contact Legitimacy in Signal Threads
Researchers assess contact legitimacy in Signal threads through a methodical appraisal of metadata, communication patterns, and cross-referenced identifiers rather than face-value trust in user labels.
They scrutinize timing, message structure, and anomalous bursts, seeking corroboration beyond self-declared contacts.
The inquiry probes for misleading verification and questions contact authenticity, emphasizing resilient evidence trails, reproducibility, and transparent criteria over assumptions or convenient labels.
Common Misconceptions About Verified Contacts Debunked
Whether verified contacts truly reflect trust, or merely reflect procedural artifacts, remains a persistent question in Signal research.
The discussion interrogates common misconceptions about verified contacts, emphasizing methodological nuance rather than sensational conclusions.
Researchers question assumed indicators of contact legitimacy, illustrating how verification signals can be influenced by protocol design, user behavior, and imperfect data—inviting disciplined scrutiny over premature certainty.
Practical Steps to Assess Contact Authenticity in Your Signals
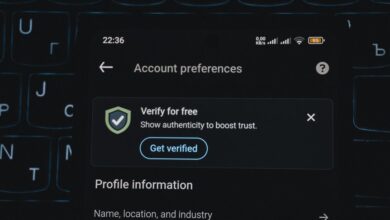
Practical steps to assess contact authenticity in Signals proceed from the prior discussion by grounding scrutiny in observable signals and protocol behavior rather than assumptions about trust. The process emphasizes verification practices, tracing message provenance, and cross-checking metadata. Analysts evaluate contact authenticity through pattern consistency, cryptographic attestations, and anomaly detection, remaining skeptical of surface guarantees while documenting evidence and rationales for each judgment.
Conclusion
In the hush of encrypted channels, the label “Signal Core Start 512-768-9531” invites certainty yet invites doubt. Researchers peel back labels to reveal process, provenance, and timing as barricades against credulity. What remains is a tightly scripted choreography of attestations, artifacts, and reproducible checks. The conclusion is neither triumph nor collapse, but a cliffhanger: can legitimacy be proven through evidence rather than claim, or do procedural echoes still wear disguises in the data? The investigation, stubbornly ongoing, lingers.