IP Address Analysis Linked to 10.7.100.58 and Feedback

The analysis centers on what reachability and path properties reveal about the IP 10.7.100.58. It considers minimal jitter, hop isolation, and stable timing to gauge internal connectivity. Feedback loops track traffic flows, timing variations, and preserved logs for pattern discovery. The approach balances privacy and governance while suggesting reproducible adjustments. The implications for security and operations invite further examination, as each finding points toward concrete refinements that may not be immediately obvious.
What IP 10.7.100.58 Reveals About Reachability
What does the IP address 10.7.100.58 reveal about reachability? The assessment isolates routing paths, latency, and hop stability to gauge IP reachability. It emphasizes Network timing as a core metric, noting consistent round-trip delays and minimal jitter across segments. Findings indicate reliable internal connectivity with predictable timing, enabling proactive adjustments for resilient, freedom-oriented network operations.
How Feedback Loops Map Traffic, Timing, and Logs
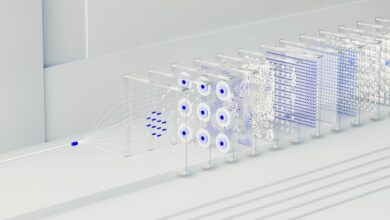
Feedback loops in network analysis systematically map how traffic flows, timing variations, and log records interrelate to reveal operational patterns.
The discussion emphasizes topic grouping, latency profiling, flow correlation, and path tracing to establish a coherent framework.
Interpreting Security Implications and Operational Context
The analysis identifies privacy risk hotspots without overreaching, enabling targeted mitigations aligned with policy.
Emphasis on data minimization constrains exposure, while monitoring informs adaptive defenses.
Clear correlations between traffic signals and governance reduce ambiguity, guiding proactive, freedom-respecting security decisions.
Turning Insights Into Practical Network Improvements
Turning insights into practical network improvements requires translating observed IP patterns into concrete engineering actions. The analysis maps IP address signals to targeted adjustments, prioritizing reachability and minimal latency. Feedback loops are established to validate changes, with logs providing evidence and traceability. Decisions emphasize reproducibility, measured gains, and risk awareness, enabling autonomous improvements while preserving operator freedom and system resilience. Continuous evaluation sustains adaptable infrastructure.
Conclusion
In a quiet lab, signals thread a single beacon—10.7.100.58—like a lighthouse cutting through fog. Reachability, once murky, emerges as a lattice of predictable paths, each hop a rung in a measured ladder. Feedback loops pulse as clockwork, mapping traffic, timing, and logs with unerring discipline. Security and operations align, footprints preserved, patterns revealed. Practical gains surface: tighter routes, lower jitter, auditable changes, and a resilient, privacy-conscious network attuned to tomorrow’s threats and needs.