Trusted Corporate Contact 0120 218 283 Professional Tech Support

Trusted Corporate Contact 0120 218 283 Professional Tech Support offers predictable response times, clear ownership, and auditable processes. It emphasizes onboarding, monitoring, and structured escalation to minimize disruption. Security and data protection are central, with governance and compliance embedded in daily operations. Costs, scope, and steps to engagement are defined up front. The framework invites scrutiny: how well does it translate into resilient, accountable service in practice, and what trade-offs emerge as needs evolve?
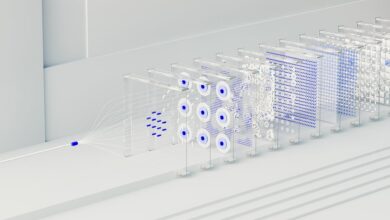
What Trusted Corporate Tech Support Looks Like
What trusted corporate tech support looks like is defined by reliability, accessibility, and accountability. It centers on predictable response times, transparent processes, and measurable outcomes. The approach emphasizes trusted onboarding and proactive monitoring, minimizing disruption and accelerating recovery. It favors structured communication, clear ownership, and documented standards, enabling teams to operate with autonomy while maintaining consistent, verifiable quality across all service interactions.
How to Assess Support Capabilities and SLAs
Assessing support capabilities and SLAs requires a structured approach: define scope, map service tiers, and identify measurable outcomes. Evaluators compare recovery time targets, uptime commitments, and response schedules. Documentation should specify escalation paths, roles, and handoff procedures. Independent testing validates performance against commitments. Clear, auditable metrics enable trusted partnerships and informed decisions without unnecessary complexity or fluff.
Security, Compliance, and Data Protection Basics
Security, compliance, and data protection form the core framework for modern tech support operations, ensuring information is safeguarded, regulatory requirements are met, and client trust is maintained.
The approach emphasizes security governance and proactive risk management, with data encryption as a fundamental control.
Clear roles, documented policies, and auditable processes support freedom through accountability, resilience, and transparent, compliant service delivery.
Making the Decision: Cost, Coverage, and Getting Started
To decide on professional tech support, organizations must weigh cost against coverage and the steps to begin.
A structured approach follows: cost assessment identifies upfront and ongoing fees; onboarding steps define access, timelines, and responsibilities; compliance basics outline regulatory alignment; data protection measures ensure safeguards.
Decision criteria balance value, risk, and readiness, enabling informed, freedom-driven vendor selection and rapid, confident start.
Conclusion
In the quiet of due diligence, the signature moment arrives: a call, a plan, a promise. The trusted corporate contact—0120 218 283—stands as a beacon of reliability, speed, and accountability. Yet the true test lies in unseen thresholds: predictable response times, auditable controls, and secure data practices that endure beyond onboarding. As decisions loom, the suspense grows—will the chosen partner deliver unwavering availability and measurable outcomes, or reveal gaps that threaten resilience? The outcome depends on proven, verifiable commitments.